
Store Shares Of Data Across Different SafeKey Devices
One unique feature of SafeKey Pro is the ability to store shares of data across different devices. This allows users to maintain shared ownership of their data and ensures that it is protected in the event that one of the devices is lost or stolen.
You can then distribute individual shares of data across different SafeKey devices, each of which serves as a secure and offline storage location for the data.
In the event that data needs to be accessed, the SafeKeys must be brought together and merged in order to decrypt the individual shares and reveal the secret data. This process ensures that the data remains decentralized and secure, as it is only accessible when all of the SafeKey devices are present.
Storing shares of data across different SafeKey devices can provide an extra layer of security and peace of mind. It ensures that your data is protected even if one of the devices is lost or stolen, and helps prevent unauthorized access to the data.
This is especially valuable for individuals and organizations that need to protect sensitive or valuable data.
Get SafeKeys for Your Team Become a SafeKey Partner
A Secure Data Protection Plan
As a business owner, it is essential to have a secure data protection plan in place to ensure the safety and integrity of your company’s data. This includes protecting sensitive financial information, customer data, and intellectual property. A data protection plan can help prevent data breaches and identity theft, which can have serious consequences for your business and your customers.
There are several steps that you can take to create a secure data protection plan for your business. One way is to invest in a secure storage solution like SafeKey, which allows for the offline storage of encrypted shares of data. This can help you protect your secure data from cyber attacks and unauthorized access.
Get SafeKeys for Your Team Become a SafeKey Partner
Traditional Data Storage Solutions Aren't Safe and Reliable
One major problem with traditional data backups and storage devices is that they often rely on centralized systems, which can make them vulnerable to cyber attacks and data breaches. When data is stored in a single location, it is at greater risk of being accessed by unauthorized individuals. This can be especially problematic for businesses that need to protect sensitive financial or customer information.
Another issue with traditional data storage is that it is often reliant on trust. For example, if you store your data on a personal hard drive, you must trust that the device will not fail or be lost or stolen. Similarly, if you use a password manager or other digital storage service, you must trust that the company managing the service will not be hacked or go out of business.
Given the increasing value of digital assets and the growing threat of cyber attacks, it is clear that we need more secure and reliable options for storing sensitive data. Solutions like SafeKey, which allows for the offline storage of encrypted shares of data, can provide a safer and more secure alternative to traditional data storage methods.
Get SafeKeys for Your Team Become a SafeKey Partner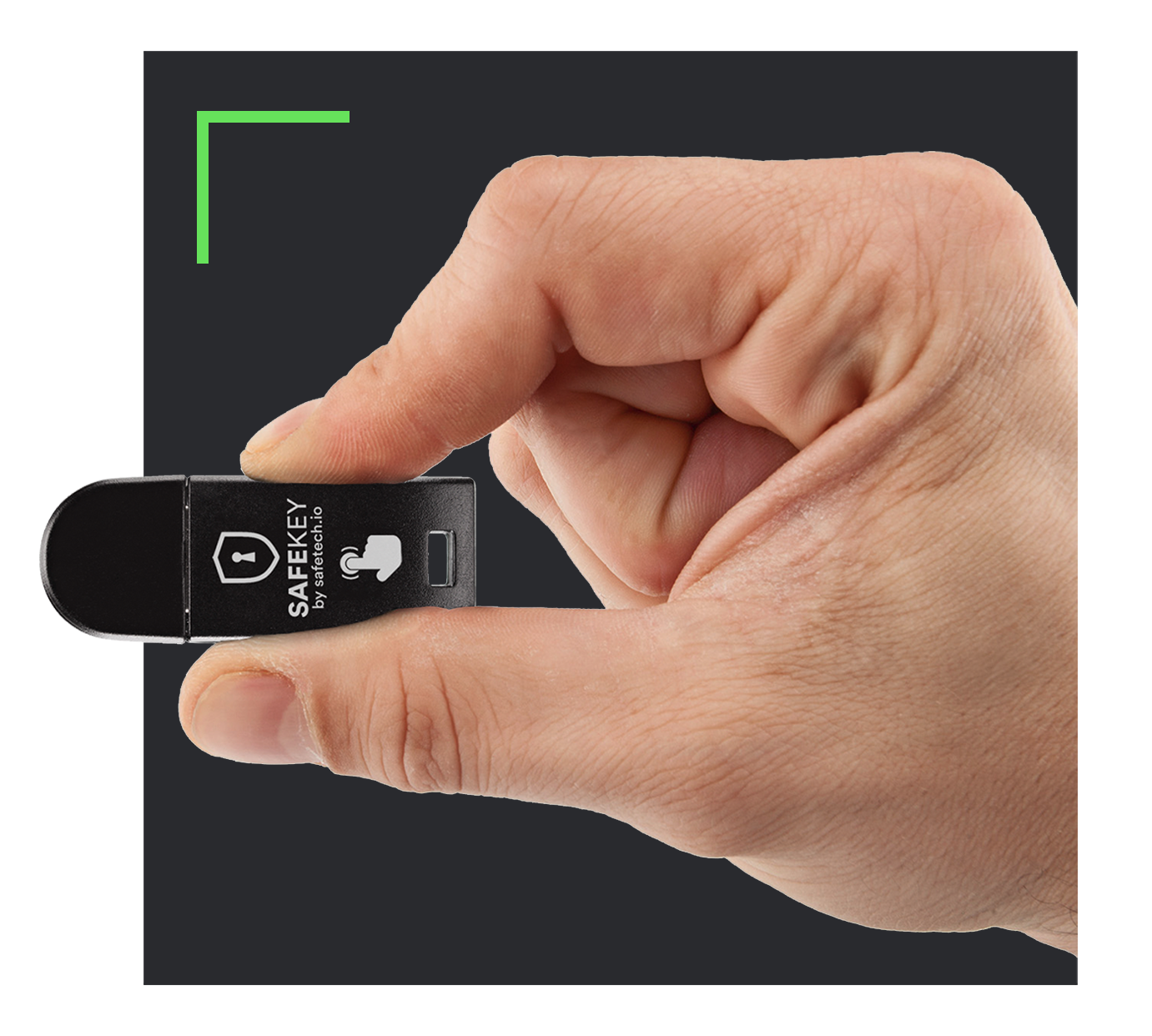
Control Your Own Data
SafeKey is a device that is designed to allow users to retain control of their sensitive data and assets. Unlike traditional methods of data storage, such as centralized digital vaults or cloud storage, SafeKey does not rely on a centralized entity to manage or store the data.
Instead, SafeKey uses a proprietary process called the Secret Shares Distribution Protocol (SSDP) to distribute the individual shares of data across different devices. This allows users to maintain shared ownership of the data and ensure that it is protected in the event that one of the devices is lost or stolen.
In order to access a backup plan created with SafeKey, the devices must be brought together and merged in order to decrypt the individual shares and reveal the secret data. This ensures that the data remains decentralized and secure, as it is only accessible when all of the SafeKey devices are present.
By using SafeKey, users can retain full control of their sensitive data and assets, rather than relying on a centralized entity to manage or store it. This can provide greater security and peace of mind, as users can be confident that their data is only accessible to those who are authorized to access it.
Get SafeKeys for Your Team Become a SafeKey Partner
Shamir’s Secret Sharing Algorithm
Shamir’s Secret Sharing Algorithm is a highly secure and flexible way to protect sensitive data. It can be used in combination with SafeKey Pro to create decentralized data backup plans that can be accessed only by those who have the necessary shares.
As a business owner, you can use Shamir’s Secret Sharing Algorithm via a tool like Inheriti®, to protect your valuable data and assets. For example, you might use it to protect the passwords or passcodes for your online accounts, or to store the private keys for your cryptocurrency wallets.
Get SafeKeys for Your Team Become a SafeKey Partner
The Benefits of Splitting Your Data Into Encrypted Shares
- Improved security: improve security by making it more difficult for unauthorized individuals to access the data.
- Flexibility: tailor the security of your data to your specific needs. For example, you can choose to require a certain number of shares in order to access the data.
- Decentralization: decentralize your data, reducing the risk of data breaches and other security threats.
- Increased reliability: ensure the reliability of the data by allowing you to create multiple copies that can be stored in different locations.
- Tamper-proof technology: encrypting secret data into shares can help protect it from tampering, as the data is secure even if one of the shares is lost or stolen.
- Improved access control: control who has access to the data, ensuring that only authorized individuals can access it.
- Increased scalability: easily scale your data protection as your business grows.
- Simplified recovery: recover data in the event of a disaster or other unforeseen circumstances.
Other Business Solutions
Experience a faster and safer login process while eliminating the need to remember and reset passwords. Increase security and reduce the risk of data breaches.
Learn moreSafeKey in combination with Inheriti® is the safest solution for your secure data backups.
Learn moreAn extra layer of security to protect your employee's accounts against hacks and phishing.
Learn moreDecentralize your data, reducing the risk of data breaches and other security threats.
Learn moreMake your employees unhackable and protect sensitive business data.
Learn moreWorkspace protection is important for businesses of all sizes, as it helps to ensure that sensitive data and digital assets remain safe and secure.
Learn more